220,000 OpenClaw Instances Are Exposed on the Public Internet
A scan of the public internet found over 220,000 OpenClaw gateway ports reachable from anywhere. Here is what attackers can do with that access, and what you should do right now.
OpenClaw is one of the fastest-growing open-source projects of 2025. Over 200,000 GitHub stars, a vibrant community, and a genuinely useful product: an always-on AI agent that connects to every messaging platform you use, running 24/7 on your own hardware.
The problem is that most people run it wrong.
What the scans show
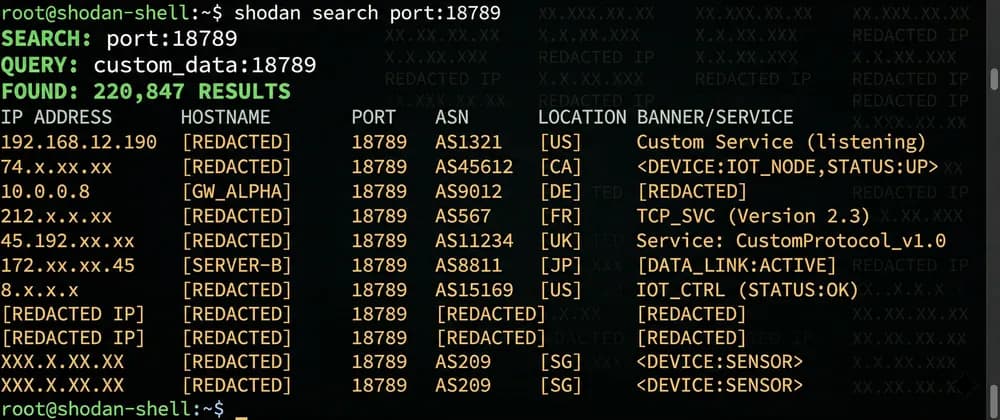
Shodan and Censys searches for OpenClaw's default gateway port (18789/tcp) return over 220,000 results. These are not private deployments hidden behind firewalls. They are instances reachable from any IP address on the internet.
220,000+ OpenClaw instances with port 18789 reachable from the public internet
Shodan / Censys, March 2026
The gateway port is OpenClaw's control plane. It exposes:
- The gateway token authentication endpoint
- The WebSocket RPC interface (config reads, config writes, log tails)
- The Control UI — a full browser interface for managing the agent
Whoever can reach that port can attempt to take full control of your agent.
What attackers do with access
ClawJacked is the name researchers gave to gateway token brute-force attacks. OpenClaw's default token validation does not rate-limit failed attempts. An attacker with network access can enumerate short or weak tokens in minutes.
Once inside, the attacker has the same privileges as the instance owner:
- Read your agent's full conversation history
- Extract every API key stored in the agent's config (Anthropic, OpenAI, Slack, etc.)
- Reprogram the agent's behavior via
config.patch - Use the agent's connected messaging accounts to send messages on your behalf
ClawHavoc is a separate category: malicious skills distributed through the community skill directory. Over 800 malicious skills have been identified. A skill runs arbitrary code inside your agent container. On an exposed instance, a malicious skill combined with a network-accessible gateway means full remote code execution.
Pre-auth voice RCE (CVE tracked in the OpenClaw GHSA list): a parsing vulnerability in the voice channel handler that triggers before authentication. If you have voice channels enabled on an exposed instance, this applies to you.
Why the default configuration is dangerous
OpenClaw is designed to run behind a reverse proxy or on a private network. Its default configuration assumes that if you can reach the port, you are already on a trusted network.
That assumption breaks the moment you expose port 18789 to the internet — which happens automatically if you:
- Run on a VPS with no firewall configured
- Use Docker with
-p 18789:18789on a public interface - Run on a home server with port forwarding set up for convenience
The OpenClaw documentation covers this. Most users do not read it before deploying.
The right architecture
The secure deployment pattern is straightforward:
- No public IP on the machine running OpenClaw — or at minimum, a firewall rule that blocks 18789 from all external sources
- Inbound access via a tunnel — Cloudflare Tunnel, Tailscale, or a self-hosted WireGuard setup. The tunnel terminates at the gateway; the port never needs to be public
- A strong gateway token — minimum 32 characters of random entropy
- Device auth enabled — OpenClaw supports pairing-based device authentication on top of the token. Enable it
This is not a new idea. It is the same architecture that database administrators have used for decades: never expose the control plane to the public internet.
What Vessel does differently
Vessel provisions OpenClaw on a dedicated GCP VM with no public IP address. Every instance is accessible exclusively through a Cloudflare Tunnel — port 18789 is never reachable from the internet. The gateway token is generated at boot, stored encrypted, and rotated on each restart.
The 220,000 exposed instances in the scan are running a different setup. They are accessible because their operators did not have time to configure the network correctly, or did not know they needed to.
That is the gap Vessel fills.
What to do right now
If you are running OpenClaw yourself:
- Check whether port 18789 is reachable from the internet:
curl -s --connect-timeout 5 http://<your-public-ip>:18789/health - If it responds, close the port immediately — firewall rule or Docker network change
- Set up Cloudflare Tunnel or equivalent before reopening access
- Rotate your gateway token
- Audit installed skills: remove anything you did not install yourself
If you would rather not manage this:

